The US-Israeli military campaign against Iran on 28 February 2026 is a live case study in modern information warfare. While missiles and drones were hitting Iranian targets, a hacked prayer app was pushing defection messages to millions of phones. Push notifications on a smartphone are a more effective delivery mechanism than leaflets dropped from aircraft. That much should be obvious, but nobody had done it in a real war until now.

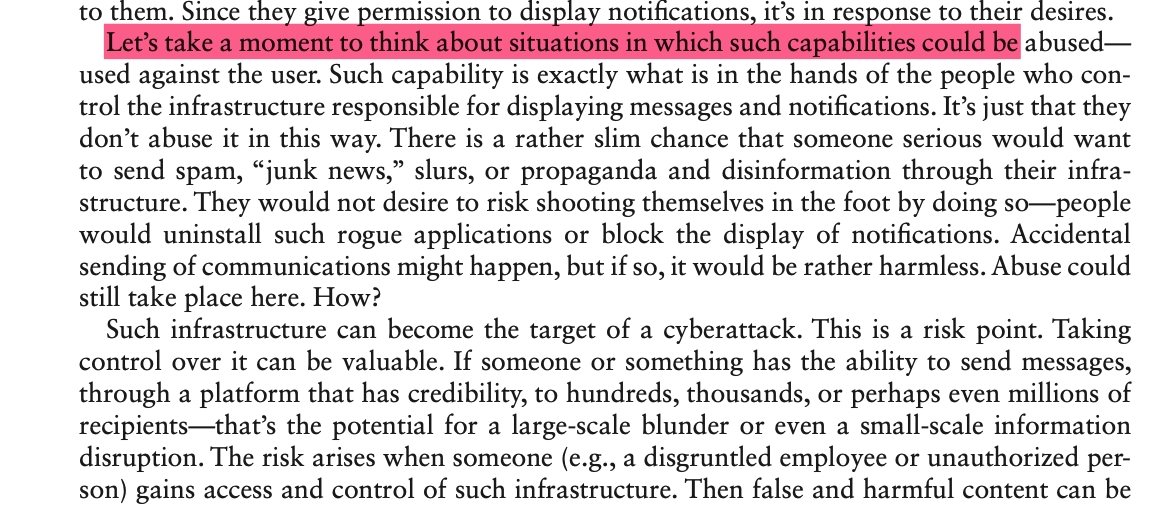
In my book PROPAGANDA (CRC Press, 2024) I predict and describe exactly this scenario. I outline the risk of hijacking push notification infrastructure as a vector for information operations at a potentially massive scale. The mechanism: whoever controls the infrastructure that sends messages to millions of devices through a trusted platform has a ready-made propaganda distribution channel. The hacking of Iran's BadeSaba prayer app, with 37 million installs, and the use of its notification system to deliver a PSYOP message synchronized with kinetic strikes calling on military personnel to defect: this is the realization of that scenario at a scale I described as potential and plausible. From hypothetical risk to operational use on the battlefield, it took just under two years.
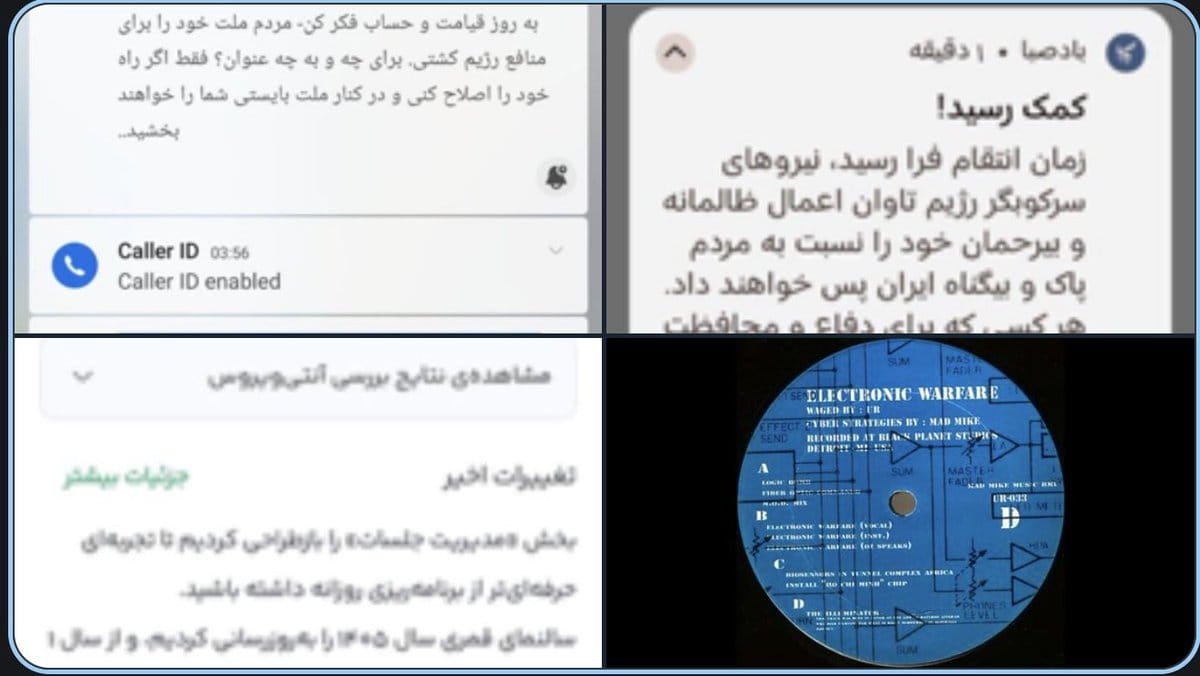
The messages arrived in Persian over a 30-minute window starting at 9:52 AM Tehran time, on the tenth day of Ramadan. First: "Help has arrived!" Then calls for soldiers to lay down their weapons, with promises of amnesty. The language closely mirrored President Trump's public messaging: immunity or consequences. The compromise of BadeSaba's notification infrastructure could not have happened on the day of the strikes. This required pre-positioning, likely weeks or months of prior access to the app's backend systems.
BadeSaba was not an isolated case. Several major Iranian news outlets, including IRNA, ISNA, Tabnak, Asr-e Iran and Rokna, were simultaneously hacked or taken offline. Some displayed replaced content: "A terrifying hour for the Ayatollahs' security forces; the IRGC and Basij have suffered a crippling blow." Independent verification during active military operations is difficult, and some of these reports may themselves be propagandistic. But the content replacement on several sites has been confirmed. The visible cyber operations almost certainly accompanied non-public offensive actions with direct operational effects. Visible and invisible operations tend to reinforce each other.
Social media amplified the information dimension far beyond Iran. Footage of missiles and drones over Dubai and the Emirates shattered perceptions of regional stability. A minor but telling detail: negative hotel reviews in the Gulf started appearing within hours. It sounds trivial, but the whole world is now watching in real time as places that marketed themselves as stable and safe turn out to be neither. European investors had been parking capital in Gulf jurisdictions for tax optimisation, banking on that stability. Now everyone has to ask a simple question: when was the last time missiles fell on a given country? For Switzerland, you need to go back to the Napoleonic Wars for a deliberate attack. For Iran and now potentially Gulf states, the answer is yesterday.
The stated objective of the campaign is regime change in Iran. The combination of air strikes, cyber warfare and information operations is a textbook case of contemporary political-military strategy. But proportionality matters. These tools alone do not dismantle a regime with redundant internal surveillance at every level. History offers no precedent for regime change achieved solely through bombardment and information operations.